Tempest Security Intelligence researcher, Filipe Xavier, found a critical vulnerability in the password manager tool Handy Password, developed by the Russian company Novosoft.
The flaw was found in the latest version of the software (4.9.3) and allows for remote code execution, giving the attacker full control of the device. Although Handy Password is still available for purchase, the current version of the software was released in May 2011, and has not gotten any updates since then. In addition, the software is not compatible with the latest version of Microsoft Windows.
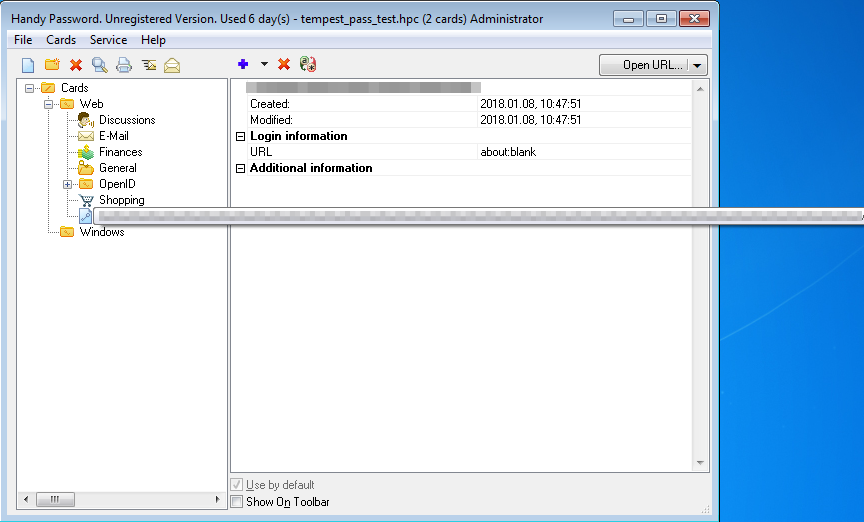
Handy Password enables the storage of credentials and personal information of users so that, when requested by sites, they are filled automatically. In addition, it makes it possible to store the password file on a remote server, allowing the user to access the credentials saved from any computer with the software installed.
The flaw identified by Tempest´s researcher affects a feature called “Open from mail box”, which allows the user to access their credentials from a remote mail server. With the feature the user downloads the password file to the computer to import it locally; however, it was discovered that Handy Password does not validate the amount of characters entered in the “Title name” field at the time of its import.
To explore the flaw, an attacker could manipulate a Handy Password file by inserting a specific combination of characters in the “Title Name” field or, in another scenario, the attacker could send a fake file, which would be interpreted by Handy Password, causing the same problem.
Handy Password is available only for Windows 2000, XP, 2003, Vista and 7. Although Novosoft does not disclose the number of its software users, an estimate was made through searches on sites that offer Handy Password for download, which counted for approximately 20 thousand users.
Tempest informed Novosoft of the vulnerability on 19th October, and once again in November. Novosoft did not respond to any of the contacts.
In December of 2017, the failure was cataloged as CVE-2017–17946.
Novosoft was founded in 1992 and, according to its marketing material, it is “one of the leading providers of integrated technology solutions and custom software development services”. The company also claims that it has been ranked by Gartner as one of the top five Russian development companies, and has clients such as IBM, Samsung America and the US Department of Energy.
