Right now Zoom is going through a situation known as the paradox of success; in which it has to deal with the problems that have accompanied the growth of its user base from 10 to 200 million and the increase in value of 90% of its shares because of the quarantine.
All of this draws a lot of attention, which has made the last 10 days quite hectic. New vulnerabilities were discovered, we learned that the product doesn’t deliver one thing that was promised, conspiratorial questions arose around the software, and a new term became a meme: zoombombing, when a stranger walks into a meeting at Zoom.
One of the questions I hear the most since we went into quarantine is: Is Zoom safe? The easy answer is: no, because nothing is 100% safe. But we have taken it upon ourselves to address the recent problems in this article in a language accessible to various audiences, as well as giving some protection tips.
Take it easy
I imagine that anyone who has had a meeting hacked must have felt pretty bad. This is perfectly understandable, but so far there is no evidence that it is possible to commit deeper attacks just from a zombombing, as long as the attacker has not collected technical information such as addresses, users and passwords presented or spoken at the meeting.
There are times in the world of cybersecurity, when a highly relevant fact is publicized, when there is a kind of gold rush among experts and the specialized press to try to extract more information from the event. A recent example was the discovery in January 2018 of two serious vulnerabilities in processors that are present in most computers and mobile devices. This discovery sparked the interest of a multitude of experts who ended up discovering a number of other problems similar to these. In the end many devices are still working today with these flaws and life went on.
We are all in a time when everyone is looking for a balance to maintain mental health in isolation, so it is common to overvalue some things to the detriment of other more important things in times of stress. We cannot neglect what has happened to Zoom in the last few days, but with calm, we will see that it is not something to be desperate about.
The Vulnerabilities
Four vulnerabilities in Zoom have been documented in the last few days. The first of these, published on March 31st, allowed a person who is already inside a meeting to send a malicious link in the product’s chat. All users with Zoom running on Windows computers who clicked on the link could be giving the attacker their login and password information, like a seed of it. This problem was fixed the next day.
On the same day, April 1, another flaw was published. In fact, a researcher discovered that the Zoom installer was using a trick that circumvented a protection of the Mac operating system to be able to install all components of the software. This is not a hackable problem, but could be considered a morally questionable “trick”. The company’s CEO stated that this would be an attempt to bring benefits to usability by balancing the amount of clicks required to install the product.
Still on the first day, TechCrunch – a well-known vehicle of the specialized press – published an article with the following catchy title: “Ex-NSA hacker divulges new zero-day for Zoom disgrace” referring to a publication by Patrick Wardle on March 30th. In the post the researcher describes two new vulnerabilities whereby an attacker who already has access to a Mac could gain further access, even spying on the computer’s webcam. The two problems were fixed on April 2nd.
Finally, members of the Canadian think tank Citizen Lab conducted research into Zoom’s encryption (which we’ll cover below) and ended up finding a vulnerability in the product’s waiting room feature – that moment when Zoom shows a video saying that the meeting hasn’t started to users who log in before it begins. The researchers noticed that Zoom was sending the room’s encryption key to any individual who had the link and accessed the waiting room. The details of the flaw and the fix were published on April 8.
Zoom learned about the first three problems from the media or social networks and so had to rush to make updates available for the first and third flaw described above and try to prevent attacks. The manipulation in the installation process on the Mac remains as it is, because although it is a crude alternative, there is no evidence of its use in Zoom attacks. Only the flaw discovered by Citizen Lab followed the process in which researchers and the manufacturer negotiate a deadline for fixing and disclosing the details.
Problems like these arise every day in a wide variety of technologies. To get an idea of the number of vulnerabilities reported, take a look at the latest edition of this bulletin, produced by a US government entity that every Monday publishes a consolidation of all vulnerabilities released in the previous week.
The time for correction may vary, but the market has agreed on a period of 90 days for the researcher to reap the benefits of the discovery and publish his research. This is present in the best practices adopted by the United States, Europe and we use this same benchmark for the vulnerabilities that the analysts here at Tempest find in several technologies. Of course, vulnerabilities that become public require quick action, and in this sense the time Zoom dedicated to solving the problems was faster than average.
Data Leak to Facebook
Before the vulnerabilities were disclosed, on March 26, came the most hard-hitting press release: Motherboard, Vice’s technology page, discovered that Zoom’s app for iOS (Iphones and Ipads) was sending data to Facebook, even if the user did not have an account on the social network.
The reason for this was that there was a Facebook development component (Software Development Kit, or SDK) built into the installation of the Zoom app, and this mechanism was collecting information from the device such as model, time zone, city, phone carrier, and a unique identifier used by the digital advertising market to send targeted ads. Clearly, for people concerned about privacy, this is a serious matter. However, we need to talk a bit about how software is produced when we ask ourselves what a Facebook component is doing inside Zoom’s app.
It is a common idea that when we ask a programmer to develop software, they write the entire system code, from start to finish. It has not been this way for more than thirty years. Of course there is coding in the development process, but one doesn’t usually spend time reinventing the wheel. So most systems are made up of original code combined with a number of other third-party components. In this case, it was enough for Zoom to remove the “Sign in with Facebook” button from its app on the 27th to no longer need the SDK.
We don’t know if Zoom’s teams studied the SDK to understand what data it collects before plugging it into their app. This is usually not the case, and integrating components without proper risk assessment is common to the development process of many systems.
This SDK may be contained in several other applications installed on your device, collecting as much information as was collected with Zoom. It may seem obvious, but it is better to say that users who have the Facebook app installed on their smartphone experience even greater and more frequent data collection.
Misleading Advertising
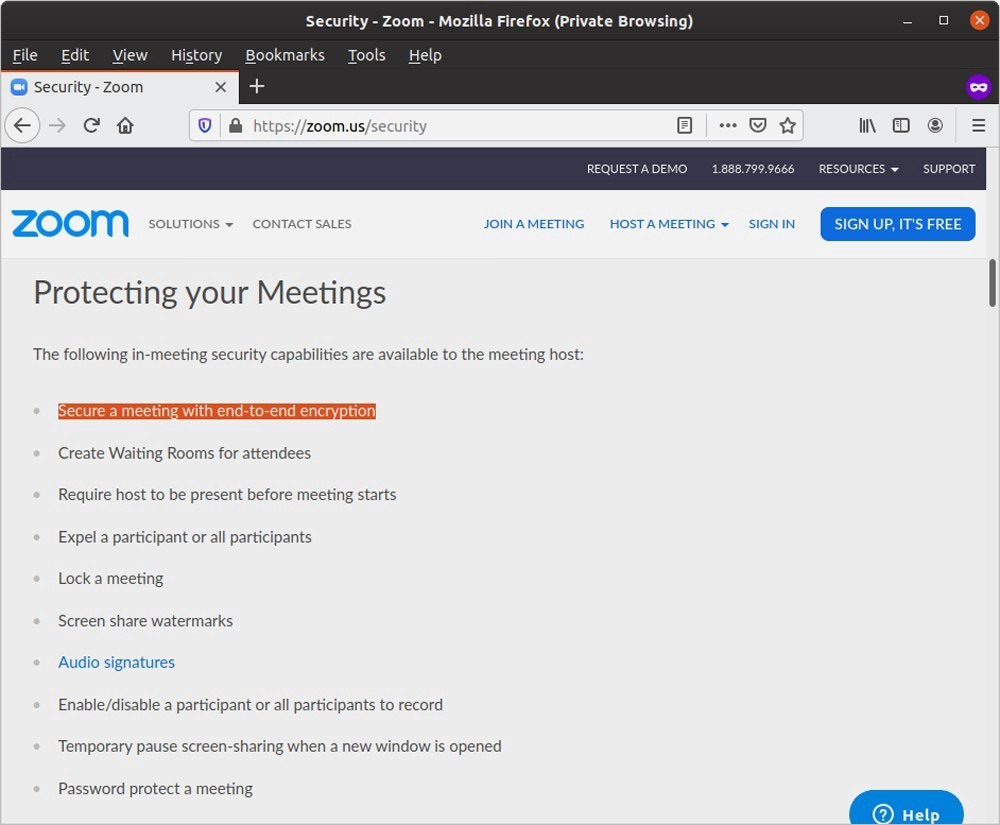
Citizen Lab’s study, published on April 3, sought to assess how robust Zoom’s encryption is and ended up identifying serious problems. The first is that the product does not have end-to-end encryption, even though it claims to do so in its promotional material.
An analogy to understand the concept of end-to-end encryption is to imagine a hotel where only the guest and his guests could enter a certain room and that, in addition, the means for generating the room keys would not be under the responsibility of the hotel. In this scenario of greater privacy, neither the hotel management, nor the government, nor the police, nor a criminal, would have the means to enter the room.
Going back to the technical perspective, this means that in an end-to-end encryption as applied in Signal and WhatsApp, for example, the content is encrypted in such a robust way that no one but the people communicating can access the content of the communication. And the beauty in that, is that what shields the communication and the management of the keys is pure mathematics.
On April 1, Zoom published a note apologizing for their misuse of the term “end-to-end encryption” and offered a somewhat oblique explanation of how encryption works in the product. In this regard, Citizen Lab’s study offers more precise technical details.
The paradox of cryptographic success
If you were a child in the eighties and nineties you will certainly have come across a rather elementary cryptographic algorithm called “p language” in which a “p” was inserted between each syllable of what was being spoken in real time ( p-un-p-ders-p-tand?). The challenge among the children was who could speak most naturally or quickly in the language of p, hiding a message from those who are oblivious to it. The algorithm demands so much brain processing in the first attempts that it was common to see children speaking very slowly while training.
Unlike people, popular computers perform very complex operations, but they do not learn by practice. They repeat instructions the same way until a human instructs them to do it another way. Since encryption is meant to make it difficult for unauthorized parties to access content, the more robust it becomes, the more work it creates for all devices involved in the process. The difficulty increases when it is necessary to encrypt voluminous media such as audio and video in real time, as happens in group calls, and it gets worse when we want the same encryption to work on multiple platforms such as computers, smartphones, and tablets with varying systems.
In other words, the demand for processing is high and everything that was revealed this week indicates that implementing end-to-end encryption would make Zoom unfeasible, as it would become very difficult to apply the same standard to, for example, support dozens of people in a meeting with audio and video enabled on devices of varying specifications. This is why WhatsApp, which has end-to-end encryption, limits its video conversations to three participants and the popular Slack, which integrates several other services, does not have end-to-end encryption.
Alternative solution
What Zoom decided to do was to apply a relatively poor encryption method. This is due to the fact that they use an obsolete form of communication in streaming audio and video transmission and have built a lot of things on top of it, like someone building a house on a flimsy foundation. The result is the need to apply specific solutions for each cracking wall until the time comes when, with time and money, one can make the necessary structural changes to the foundation. That is, until the time comes when new technologies emerge and make the “foundation” that was just updated obsolete and the cycle starts all over again. This kind of thing happens in many technologies, and more often than you might think.
What the researchers identified was that Zoom uses a robust algorithm but with a relatively weak key and that its distribution was done using a very poor method that leaves traces of the key details. So an attacker could collect the audio and video of the meeting while it was taking place, break the security of the key and decrypt the material he collected.
And this attack would come from where? To be successful, the attacker needs to identify the communication flow in the traffic. The best places to do this would be on the same network that the meeting participant is on or within Zoom’s network. And now it is necessary to be very calm not to fall for conspiracy theories.
China
The Citizen Lab study indicated that Zoom would have 3 companies and 5 servers operating in China. It is common for technology companies to spread servers around the world to have contingency and avoid performance problems in the connection. But the Chinese servers were used even when the conversation was between people in the United States and Canada. If there was not a general breakdown in the American servers that justified the traffic through China, this would be strange to say the least.
Regarding the Chinese subsidiaries, it is typical that various companies look for ways to maximize profit in places with cheaper labor. However, no information has yet been released that might indicate Chinese state interference in Zoom’s subsidiaries.
From these findings, the folks at The Intercept published a story on the 7th about the case, saying that China has an authoritarian political arrangement that is reflected in its management of the Internet, that Zoom does not have a culture of transparency regarding government requests, documenting them in periodic reports on the subject, as Facebook, Google and Microsoft do. It could therefore more easily succumb to Chinese government interference.
It is correct that Chinese interference in the Internet is very deep, being based on mass surveillance, very strict access control and censorship. However, we have to consider that most of Zoom’s servers are in the United States and, thanks to Edward Snowden’s leaks, we know that the NSA has a very advanced spying structure that, among several other initiatives, monitored, for example, Skype calls.
Those who dedicate themselves to cybersecurity read almost on a daily basis research about espionage and surveillance campaigns conducted by governments. Could it be that China is monitoring Zoom’s servers? Of course. But the same goes for other countries that have an established espionage structure, such as the United States, Israel, Iran, Russia, North Korea, and several others. Go to this site from the Council of Foreign Relations, filter the list by State Sponsor (country that funds the attacks) and see a timeline catalogued by each country.
Do these countries violate people’s privacy? Regrettably yes. But any of us can make life difficult for those who want to attack us, so in the next section I close this long article with some recommendations for using videoconferencing systems.
Meeting without meddlers
f you have followed me this far you must have realized that Zoom has weaknesses, but that weaknesses can be found many technologies. Another thing is that there are well-organized and resourceful groups that can attack Zoom, but they also have the ability to attack many other systems. In other words, the problem of security and privacy is more complex than pointing the finger at a single manufacturer.
Of all the materials I have cited in this article, one excerpt from Citizen Lab’s study is important for you to decide for yourself if Zoom is safe for your reality:
“For those who use Zoom to keep in touch with friends, hold social events, or organize courses or lectures that they might otherwise hold in a public or semi-public place, our findings should not necessarily be of concern.”
Given everything that happened in these days, it was possible to see that Zoom has acted quickly to correct the problems, but I hope to have made it clear here and in other texts of this series, that security is also a matter of behavior and this goes through taking incorporating protective attitudes to the day to day, so I share here some recommendations that can help you protect your meeting in various video conferencing systems:
1 — Keep your videoconferencing software up to date
Software updates fix several problems and even close loopholes used by attackers.
2 — Use passwords for your meetings
Many videoconferencing systems allow you to set a password for each meeting. This prevents intruders from entering the room without you noticing.
3 — Be aware of who is in the room
It is worth checking if all the people in the room are really the ones you invited. Ask the shy ones to open the camera, because an intruder can enter the room under the name of a guest. It is also good to check if the guests have changed from time to time.
4 — Avoid inviting through links
Yes, we agree that sending the link of the meeting to the guests is very practical, but the danger usually lies in the convenience. Authentic links can leak out and fall into the hands of malicious people in many ways, making it possible to break into the room, even if you have set a password for the meeting.
Fake links are used in a variety of other attacks, so if your team does not share this information, they are less likely to fall victim to a malicious link attack.
Give preference to sending to the guests only the number or name of the meeting and the password.
5 — Beware of selfies and screen prints
Some videoconferencing systems show meeting data that can be useful to an attacker – Zoom used to show the meeting number on the screen, but removed this information in the last update, published on the 8th. It is very important to blur or crop this data from the screenshots before posting.
