The cybercrime history is going through a moment of accumulation of weapons in large arsenals; there is a buildup of massive cyber weapons in espionage operations, often attributed to nation-states. While some of these stockpiles yield almost cinematic stories, for example in the case of the Equation Group, there are also threats with more common purposes, such as those that target the theft of payment card data, but which are also based on amassing tools and malware in quantities which are as large as intelligence agencies.
In a routine analysis, members of Tempest’s Threat Intelligence team found a set of malware samples, which, at first glance, seemed to be linked to a traditional attack campaign against Brazilian merchants using Point of Sale (POS) systems. Bearing in mind that it is part of the attacker’s strategy to hide large operations in seemingly ordinary behaviour, the researchers went deep into the discovery and found a major operation, which, in four years, had maintained dozens of tools and hundreds of malware in its arsenal and had accumulated more than 1.4 million payment card data (credit, debit, food and meal cards).
Named by researchers at Tempest as HydraPOS, the fraudsters’ operation has several “heads”, which, at the beginning of the attacks, aimed only at stockpiling payment card data by exploiting supermarket systems. However, over the years, it has incorporated the collection of bank data and e-commerce access credentials into its criminal activity.
The HydraPOS operation is made up of several pieces of malware — found in hundreds of different builds and versions — and a handful of third-party and malware tools known as Kaptoxa — used in the attack against the large retailer Target in 2014 and also known as Trojan.POSRAM — and other malicious code hitherto unidentified or published by the industry.
Techniques for infection
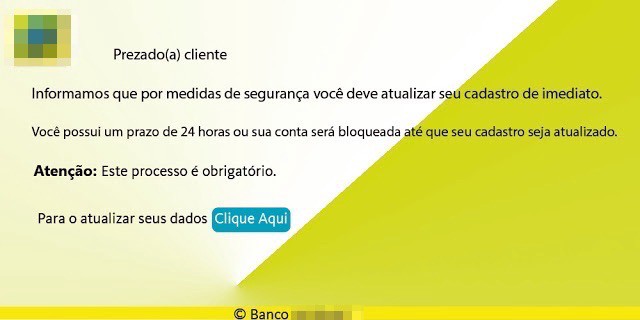
The process of infection by HydraPOS is based on a vast scan, often involving the entire broadband service range of Brazilian telecommunications companies. This activity uses tools known as VNC-Scanner, or another for the same purpose, but developed by the threat actor. These tools search for commonly used remote access services (VNC, RDP, Radmin, and SSH) that are incorrectly configured or are based on outdated software versions. Targets identified at this stage are subjected to brute-force attacks to gain access to passwords or to exploit previously documented vulnerabilities. Depending on technical specificities, or other criteria, HydraPOS operators also use phishing attacks to infect victims.
In the merchant’s network
From the moment the attacker gains access to the victim’s computer, there are a variety of paths that HydraPOS operators can take to install new malware, extract data, and maintain persistence in the environment.
Connections to targets through remote administration tools by themselves allow for a series of operations, depending on the access privilege gained by the attacker.
In cases in which the infection vector occurs through phishing, a malicious file is sent to users, which, when activated, allows for the opening of a channel via Remote Desktop with administrative privileges, among other functionalities.
Depending on the characteristics of the environment, the logic present in the latest version of HydraPOS code defines which tools will be used to collect access credentials and payment card data. Researches had identified cases in which the data collection was based on Kaptoxa – malware active since 2013 and sold in darknet forums – which was developed to recognize and extract card data being processed in the memory of the computers at the time of transaction.
Although much of the communication in the process of a card transaction is encrypted, POS software naturally needs to decipher the information in the transaction authorization process. The memory-scraper malware type, such as Kaptoxa, is designed to identify which spaces in memory will be allocated with information of interest to the attacker. In this way, these malware wait for the space to be filled with the information of interest and save that data in files to be later sent to a command and control server.
It was found, through the analysis of more recent artefacts, that the memory scraping activity was later incorporated into the HydraPOS code, suggesting that, at some point, the use of Kaptoxa was abandoned or reduced.
HydraPOS operators also use other third-party malware to obtain target data. In the binary named “Track 2 sniffer.exe“, it was identified the Win32/Dexter (also called Poxters), which has keylogger and memory scraping functions.
Malware developed by the attacker himself are also used, such as the keylogger that uses the filename “pdv.exe”, the memory-scraper that uses the filename “explorer.exe” and the e-commerce credential collector that uses the filename “win.exe“.
Many of these malware send data to command and control servers. However, depending on the specificities of the victims’ infrastructure, this information could also be e-mailed or selected and retrieved remotely and on demand by the attacker.
Command and Control Servers (C&C)
Tempest’s Threat Intelligence team was able to identify seven servers in use by the attacker; part of these repositories stored 1,454,291 records of payment card data, which evidence pointed to an accumulation since 2015. The total number of stolen data can be much higher, since, through the investigation and intelligence work in open source data, evidence was found suggesting that HydraPOS operators have been active at least since 2013. The possibility of the data being collected on demand, or sent by e-mail also supports the thesis that fraudsters might have access to more information than those stored in their C&Cs.
Another part of the C&Cs contained the massive arsenal available to operators. Several versions of other artefacts have been identified, covering various distributions of legitimate use tools (such as those used for remote administration), brute-force attack mechanisms, and tools for collecting email addresses.
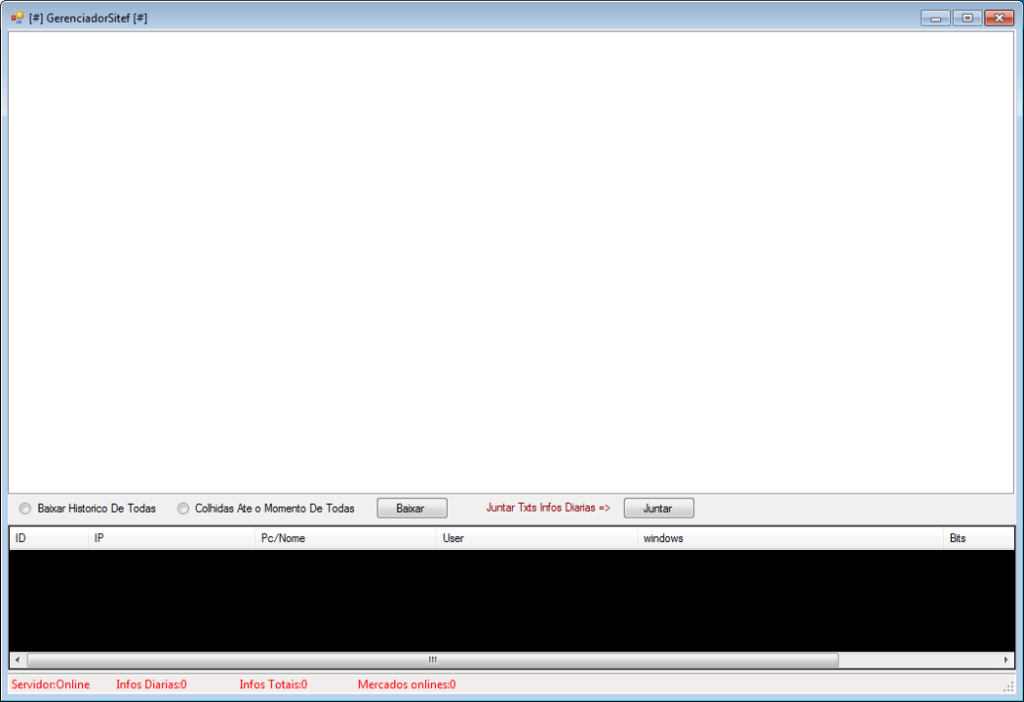
In addition, the repositories contained tools developed by HydraPOS operators to handle the large volume of information and targets, such as the “FindInfoTxt” — which classifies payment card data according to the service code, separating more valuable and larger cards limits, such as platinum cards, from others with less value — or the “Gerenciador Sitef”, which operates as a control panel to check status and send commands to infected machines.
Further details on the HydraPOS arsenal are available in the appendix below.
How to prevent attacks similar to HydraPOS
Operations such as HydraPOS take advantage of three failures that can be found in companies of all sizes, but which are very common in environments where computers are used for a minimum set of features, such as the supermarket checkouts:
- use of misconfigured remote administration tools,
- use of fragile passwords,
- absence of a security-oriented configuration pattern of the operating system and its applications.
In these environments, the more geographically dispersed the stores are, the more necessary it is to use tools for remote administration such as VNC, Remote Desktop or Radmin. On many occasions, access to the machines is made by a large number of employees, sometimes outsourced, and with a high turnover level. Thus, the password setting for remote administration tools, when it exists, is often made for the rapid absorption of the teams. The result is the definition of fragile passwords, shared among all support analysts and easily identified by brute-force tools.
To avoid this scenario, it is important to choose remote access solutions that centrally allow for the granting and revocation of access for each support analyst, thus avoiding the sharing of passwords between people. It is also important to adopt two-factor authentication solutions, not only depending on the user and password to access network resources, but also on other factors such as tokens, biometrics, etc.
As important as setting standards for the use of passwords and other authentication mechanisms, it is essential to maintain up-to-date systems and establish standards for the configuration of all machines. Updates should not be limited to the operating system, but they need to cover all other applications, and the standards should cover all configurations to make them more secure.
In addition, it is important that all employees be trained on how to identify suspicious messages, common to phishing attacks. There are several ways to train users about it, like educational phishing platforms to train employees regarding the fact that this is one of the most common threats in the world.
Appendix and Indicators of Compromise
Below some tools and artefacts are described, as well as indicators related to HydraPOS
Legitimate remote administration tools used by attackers:
- RealVNC: Client / Server VNC.
- ThighVNC: Client / Server VNC.
- NVNC: Server VNC.
- Ammyy: Client / Server for remote administration.
- Bitvise: Client / Server SSH.
Malicious tools developed by third parties:
- VNC-Scanner: scan tool that searches for vulnerable VNC machines and exploits vulnerabilities in this service.
- Fast RDP Brute: tool used in brute-force attacks to obtain access credentials on RDP systems.
- VUBrute: tool used in brute-force attacks to obtain access credentials on VNC systems.
- DUBrute: tool used in brute-force attacks to obtain access credentials on RDP systems.
- LameScan: tool used in brute-force attacks to obtain access credentials on Radmin systems.
- Advanced IP Scanner: network scanner and Trojan installer on RDP and Radmin systems.
- Sanmao Email Collector: collector of email addresses on websites.
- Sanmao Email Scraper: collects email addresses in search tools.
- Sanmao SMTP Mail Cracker: tool used in brute force attacks for email.
Tools developed by HydraPOS operators:
FindInfoTxt: tool to classify card data according to the Service Code, extract BINs (Bank Identification Number) and delete repeated tracks. No detection by VirusTotal.
- MD5: 3d05a4d2ddf9fa1674579b15d5980c26
- SHA1: 24ce8ff328b44658f0db21dac25f109c57eeea5e
- SHA256: d88b82e936adf47778826dd23886c9288e807f389a242bfb5a0f6e4fdc8674ac
Gerenciador Sitef: control panel for real-time visualization of infected merchants’ computers. It also sends commands to the infected machines. No detection by VirusTotal.
- MD5: e4755ce3c7ee50a08a8902e9fa978588
9f82da18f8591749e212efe6dccca45b
7c513ea612f05774593c916487791bb7
31dbef6f3027a4048d8dabc756172043
a172ebf8d867282027db1ef0cd08a815
8805d1d9530c1b9943d1089715e81faf - SHA1: 903e41db1daa11665b28d06e8b7a417e367b5fe9
637820e583b5de7f17fa674341e2fc0448269758
f809c37bb465a69d37b46cfb902ef9336c3bef19
fce01e84cdca3315e1955ec7a97261546a530ca7
c29e69d088f6836506d529d51dbd6960f6e173c2
385026cc6e70621820db13d475a24292aa72bdeb - SHA256: 90d0ccb265b27fe8e656058927e044424652c9086e42f93fdb112744e5ea4170
bca53f93de2ad7421781190846ba9e980e1fcfc6b9d9e9dfbb8bb90c142b7510
bba21698e0463cf11cb4ee3c50b85be3cc435ccbf3d95a42e866dc6afc1c4426
c336a423dce1a1a9189d4dd1810f91d2556eac89df3b2a998805230104f1cfb0
fbda9405800022dfb2fb774812204dc757b56857c646c65e6d603ffb7bd38066
3a654e636c27b724398a878dcab074888870d7fa97208bca1caf25cffdeb7078
LRemoto: tool that allows the infected computer to connect and download other malware components or updates. No detection by VirusTotal.
- MD5: 331b0647df20c7522ceee719a040bacc
f4792f398c11f658247ee1a74f4edb49 - SHA1: a0957bf849a3095767abe42fb38404c245290dca
78b0c3a3b8290f94689b4d29dd24b29b260113a1 - SHA256: 9df8233c78ced7e05d8a55781378901091d364ccdfb6b9d25a6e18eb7a72d9c4
6e7cd73ddad3644dd3b485857040d8d300323941e5712304c53fa5118feab871
Scanner: scan tool that identifies IP addresses that are running VNC and RDP services. It also has brute-force functionality. No detection by VirusTotal.
- MD5: 8b729325e03409184bebc02d61502a9f
49f88b841399fe3823c68062385810cb - SHA1: 6009b29d22ed110b870a21724072218a2619c6b1
479aae86dd94e5492629473eeaf3253da27d3c9a - SHA256: 6743c785377c3c1979df989dea5ef8e7bc82cb29d90aae581413bfa1880efbb3
c070e1a59ada494c123a205ffc7f34538ca35d75f387f1ef4ff103bc38c5559a
Windows Explorer: tool for sending SPAM. No detection by VirusTotal.
- MD5: 23b1aa4ac397010daa1fb82de273329c
f2ec2e7b63454ebf91a83e963ac12076
f1c2c265a7d02975176d4d4080ffd991
355db373919f43891b65c22f8dffa724
00daf6c9021fabac564052ed028ff430
f41d57ea16e0bc4e4af5b6a995076e71 - SHA1: 8a6e9d42d731c6c259c3fff8fcc93b228fb4c04e
8888247f5db0ccac39754bdda233dc62e8849399
374a436061c39b8fcaebbb31f27da1cfd85e514b
978c51479e6663be0879fd1829b9571486de78e1
a8e6df5b10419ff1ff041e95f5838d5dc3c69dee
94393ba45e1a75fee4b85c33dd19aa5dd1f3f985 - SHA256: c08b7964dc5b7512e6e9054da389c4226fdb0a56dea26c69d173bee4d8b56e92
e43a99c8cba91ec7e3c33e1def1f1add8be3fe76348232c5d4bae994714ba0a1
f40a49d723034dc79bd4c93ec8562b1dc836fd5f8fc4a2be8c3a07686653d5c4
0271b7248d844aa63acdee56557ce6c79e1c730d7fc891aaac76d033ec8c07f6
b7bfba4c9092369a13dd758b30b8ca38672a287a7c84554c02e47c693ff8f7b0
9e531f04bf9142a8d96868efb9995a784aa8e1fe1ddbcf304098bbc0c67994cc
Olhar: tool that manages a list of infected computers. Detection ratio in VirusTotal: 5/63.
- MD5: e284a2aac9ad1523564aecc11f6c0680
- SHA1: 6483934ce8363694e81eec473adaa29a0905e601
- SHA256: d0cd4a6b01ce81ec8030fbb5b4de9437106a276602cbd590b5680ee3e0212aa8
Third-Party Malware:
- Kaptoxa: memory-scraper malware
- Win32 / Dexter: keylogger and memory-scraper
Malware developed by HydraPOS operators:
Adobe.exe: Payment card data collector and e-commerce credentials. No detection by VirusTotal.
- MD5: bd0aca51fbde462328cafab83dd9d619
- SHA1: b9a2c27b9e72c6ee38927f2a8ba9bf20725dbffc
- SHA256: 8709cc4ee0a0c3040a173f58521dda0fe436af7e0fbb69f59169cebbf3c1ddac
pdv.exe: keylogger. No detection by VirusTotal.
- MD5: 8c745dd89a6de372a49fe9faa6d614a2
- SHA1: 7d1d7a490ba1362d90dc569d2471af56b38ac8b0
- SHA256: 5bf208da4e4bb3a1c6403f370badb30f50ffc0d26b11744bb66d3450a68e51fd
explorer.exe: memory scraping malware. Detection ratio in VirusTotal: 29/63.
- MD5: d4127862bf705de3debbdbce99b70bed
- SHA1: 54f10b1c505183459b47da596a02863de619a22d
SHA256: d1255ac2458c778de0268281ea2f2e54b55af69418aa86f8ba3f61a746cc9988
Win.exe: kkeylogger and payment card data collector and e-commerce credentials. Detection ratio in VirusTotal: 19/63.
- MD5: ba07fbcd7f2a12957e81939bb88d2a6b
- SHA1: 0b2cf34b1af46607e19a18ddac9b2fefcb29eca1
- SHA256: 2f1442c01baa1cfcc64c96802707a5d7ac16891c7e2fbbc4f3f863d19f64476e
Anexo Pdf(167371371).exe: used to download and activate another malware. Detection ratio in VirusTotal: 32/63.
- MD5: 8b0fb09fb1ed82a88e9e5f1e69823afa
- SHA1: 3d28362bde5f1e99131a2107df80462a58fa00f7
- SHA256: 2a2af38cbfa51d56aa7bebb357825d8e661a532e043ef614bf9c473df6a8e8b8
IP Addresses
- 66[.]220[.]9[.]50 — Port: 21/TCP
- 216[.]244[.]71[.]135 — Port: 1/TCP
- 216[.]244[.]95[.]10 — Ports: 1 and 7
C&C URLs
- hxxp://m4godoc .esy.es
- hxxp://envioip .esy.es
- hxxp://infectbbb .esy.es
- hxxp://www.gidlinux .ninja
